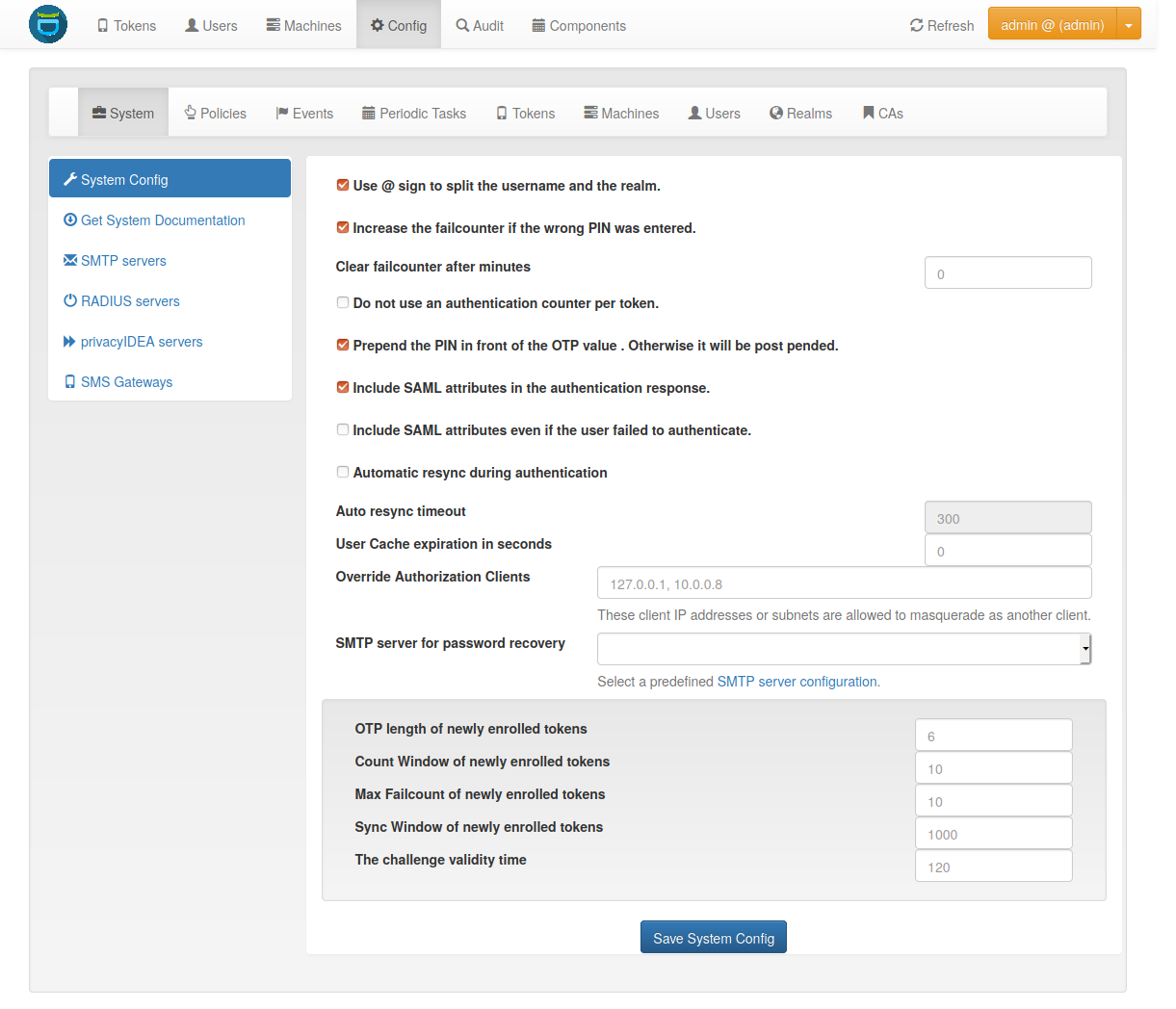
5.3. System Config¶
The system configuration has three logical topics: Settings, token default settings and GUI settings.
The system config¶
5.3.1. Settings¶
5.3.1.1. Use @ sign to split the username and the realm.¶
This option defines if the username like user@company given during authentication should be split into the loginname user and the realm name company. In most cases this is the desired behavior so this is enabled by default.
But if users log in with email addresses like user@gmail.com and otheruser@outlook.com you probably do not want to split.
How a user is related to a realm is described here: Relate User to a Realm
This option also affects the login via the Authentication endpoints
5.3.1.2. Increase the failcounter if the wrong PIN was entered.¶
If during authentication the given PIN matches a token but the OTP value is wrong, the failcounter of the tokens for which the PIN matches, is increased. If the given PIN does not match any token, by default no failcounter is increased. The latter behavior can be adapted by this option. If it is set and the given OTP PIN does not match any token, the failcounter of all tokens is increased.
5.3.1.3. Clear failcounter after minutes¶
If the failcounter reaches the maximum the token gets a timestamp, when the max fail count was reached. After the specified amount of minutes in this option, the following will clear the failcounter again:
A successful authentication with correct PIN and correct OTP value
A successfully triggered challenge (Usually this means a correct PIN)
A 0 means that the automatic clearing of the fail counter is not used.
Note
After the maximum failcounter is reached, new requests will not update the mentioned timestamp.
5.3.1.4. Do not use an authentication counter per token.¶
Usually privacyIDEA keeps track of how often a token is used for authentication and how often this authentication was successful. This is a per token counter. This information is written to the token database as a parameter of each token.
This setting means that privacyIDEA does not track this information at all.
5.3.1.5. Prepend the PIN in front of the OTP value.¶
Defines if the OTP PIN should be given in front (pin123456)
or in the back (123456pin) of the OTP value.
5.3.1.6. Include SAML attributes in the authentication response.¶
This option defines, if during a SAML authentication request additional SAML attributes should be returned. Usually an authentication response only returns true or false.
The SAML attributes are the known attributes of a user that are defined in the attribute mapping of the user resolver and possible custom user attributes, like email, phone, givenname, surname or any other attributes the resolver provides. For more information read UserIdResolvers.
In addition you can set the parameter Include SAML attributes even if the user failed to authenticate.. In this case the response contains the SAML attributes of the user, even if the user failed to authenticate.
5.3.1.7. Automatic resync during authentication¶
Automatic resync defines if the system should try to resync a token if a user provides a wrong OTP value. AutoResync works like this:
If the counter of a wrong OTP value is within the resync window, the system remembers the counter of the OTP value for this token in the token info field
otp1c.Now the user needs to authenticate a second time within the time-interval given in Auto resync timeout with the next successive OTP value.
The system checks if the counter of the second OTP value is the successive value to
otp1c.If it is, the token counter is set and the user is successfully authenticated.
Note
AutoResync works for all HOTP and TOTP based tokens including SMS and Email tokens.
5.3.1.8. User Cache expiration in seconds¶
This setting is used to enable the user cache and
configure its expiration timeout. If its value is set to 0 (which is the default value),
the user cache is disabled.
Otherwise, the value determines the time in seconds after which entries of the user
cache expire. For more information read User Cache.
Note
If the user cache is already enabled and you increase the expiration timeout, expired entries that still exist in the user cache could be considered active again!
5.3.1.10. SMTP server for password recovery¶
Specify the SMTP server configuration which should be used for sending password recovery emails.
5.3.2. Token default settings¶
Note
The following settings are token specific values which are set during enrollment. Some of these values can be overridden by policies or events during rollout.
5.3.2.1. OTP length of newly enrolled tokens¶
This is the default length of the OTP value. If no OTP length is specified during enrollment, this value will be used. This affects all OATH-based tokens like SMS, Email, TOTP and HOTP.
5.3.2.2. Count Window of newly enrolled tokens¶
This setting defines how many OTP values will be calculated during an authentication request to check for a match.
5.3.2.3. Max Failcount of newly enrolled tokens¶
This setting defines the maximum failcounter for newly enrolled tokens. If the failcounter exceeds this number the token can not be used unless it is reset.
Note
In fact the failcounter will only increase up to this maximum failcount (Maxfail).
Even if more failed authentication request occur, the failcounter will
not be increased.
5.3.2.4. Sync Window of newly enrolled tokens¶
This setting defines the synchronization window for newly enrolled tokens. The window defines how many OTP values will be calculated during a resync of the token.
Note
In case of HOTP token, this is the amount of steps that will be calculated from the current token counter onwards. For TOTP token, the number of steps will be multiplied with the timestep of the token and this interval will be checked before and after the current time.
5.3.2.5. The challenge validity time¶
This setting defines the timeout for a challenge response authentication. If the response is received after the given time interval, the response is not accepted anymore.
