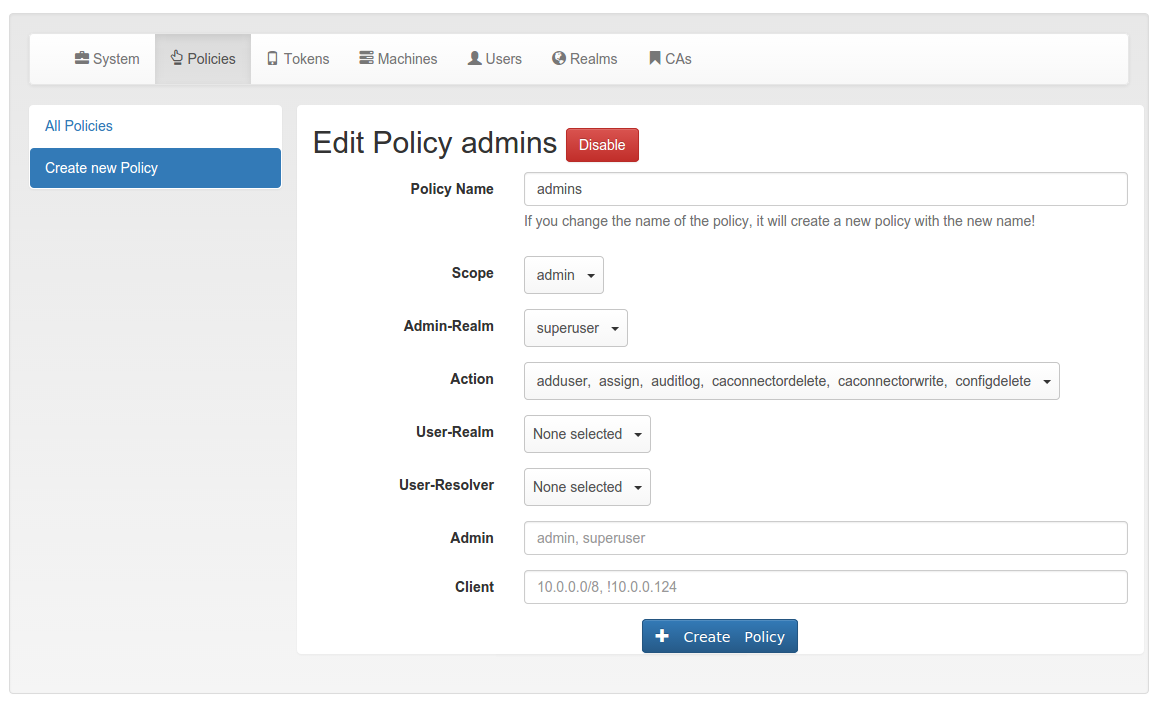
7.1. Admin policies¶
Admin policies are used to regulate the actions that administrators are allowed to do. Technically admin policies control the use of the REST API Token endpoints, System endpoints, Realm endpoints and Resolver endpoints.
Admin policies are implemented as decorators in Policy Module and Policy Decorators.
The user in the admin policies refers to the name of the administrator.
Starting with privacyIDEA 2.4 admin policies can also store a field “admin realm”. This is used, if you define realms to be superuser realms. See The Config File for information how to do this.
This way it is easy to define administrative rights for big groups of administrative users like help desk users in the IT department.
All administrative actions also refer to the defined user realm. Meaning an administrator may have many rights in one user realm and only a few rights in another realm.
Creating a policy with scope:admin, user:frank, action:enable
and realm:sales
means that the administrator frank is allowed to enable tokens in the
realm sales.
Note
As long as no admin policy is defined all administrators are allowed to do everything.
The following actions are available in the scope admin:
7.1.1. init¶
type: bool
There are init actions per token type. Thus you can
create policy that allow an administrator to enroll
SMS tokens but not to enroll HMAC tokens.
7.1.3. disable¶
type: bool
Tokens can be enabled and disabled. Disabled tokens can not be
used to authenticate. The disable action allows the
administrator to disable tokens.
7.1.4. revoke¶
type: bool
Tokens can be revoked. Usually this means the token is disabled and locked. A locked token can not be modified anymore. It can only be deleted.
Certain token types like certificate may define special actions when revoking a token.
7.1.5. set¶
type: bool
Tokens can have additional token information, which can be viewed in the Token Details.
If the set action is defined, the administrator allowed
to set those token information.
7.1.6. setOTPPIN¶
type: bool
If the setOTPPIN action is defined, the administrator
is allowed to set the OTP PIN of a token.
7.1.7. setMOTPPIN¶
type: bool
If the setMOTPPIN action is defined, the administrator
is allowed to set the mOTP PIN of an mOTP token.
7.1.8. resync¶
type: bool
If the resync action is defined, the administrator is
allowed to resynchronize a token.
7.1.9. assign¶
type: bool
If the assign action is defined, the administrator is
allowed to assign a token to a user. This is used for
assigning an existing token to a user but also to
enroll a new token to a user.
Without this action, the administrator can not create a connection (assignment) between a user and a token.
7.1.10. unassign¶
type: bool
If the unassign action is defined, the administrator
is allowed to unassign tokens from a user. I.e. the
administrator can remove the link between the token
and the user. The token still continues to exist in the system.
7.1.11. import¶
type: bool
If the import action is defined, the administrator is
allowed to import token seeds from a token file, thus
creating many new token objects in the systems database.
7.1.12. remove¶
type: bool
If the remove action is defined, the administrator is
allowed to delete a token from the system.
Note
If a token is removed, it can not be recovered.
Note
All audit entries of this token still exist in the audit log.
7.1.13. userlist¶
type: bool
If the userlist action is defined, the administrator is
allowed to view the user list in a realm.
An administrator might not be allowed to list the users, if
he should only work with tokens, but not see all users at once.
Note
If an administrator has any right in a realm, the administrator is also allowed to view the token list.
7.1.14. checkstatus¶
type: bool
If the checkstatus action is defined, the administrator is
allowed to check the status of open challenge requests.
7.1.15. manageToken¶
type: bool
If the manageToken action is defined, the administrator is allowed
to manage the realms of a token.
A token may be located in multiple realms. This can be interesting if you have a pool of spare tokens and several realms but want to make the spare tokens available to several realm administrators. (Administrators, who have only rights in one realm)
Then all administrators can see these tokens and assign the tokens. But as soon as the token is assigned to a user in one realm, the administrator of another realm can not manage the token anymore.
7.1.16. getserial¶
type: bool
If the getserial action is defined, the administrator is
allowed to calculate the token serial number for a given OTP
value.
7.1.17. losttoken¶
type: bool
If the losttoken action is defined, the administrator is
allowed to perform the lost token process.
To only perform the lost token process the actions copytokenuser
and copytokenpin are not necessary!
7.1.18. adduser¶
type: bool
If the adduser action is defined, the administrator is allowed to add
users to a user store.
Note
The user store still must be defined as editable, otherwise no users can be added, edited or deleted.
7.1.19. updateuser¶
type: bool
If the updateuser action is defined, the administrator is allowed to edit
users in the user store.
7.1.20. deleteuser¶
type: bool
If the deleteuser action is defined, the administrator is allowed to
delete an existing user from the user store.
7.1.21. copytokenuser¶
(TODO) Not yet migrated.
type: bool
If the copytokenuser action is defined, the administrator is
allowed to copy the user assignment of one token to another.
This functionality is also used during the lost token process. But you only need to define this action, if the administrator should be able to perform this task manually.
7.1.22. copytokenpin¶
(TODO) Not yet migrated.
type: bool
If the copytokenpin action is defined, the administrator is
allowed to copy the OTP PIN from one token to another without
knowing the PIN.
This functionality is also used during the lost token process. But you only need to define this action, if the administrator should be able to perform this task manually.
7.1.23. getotp¶
(TODO) Not yet migrated.
type: bool
If the getserial action is defined, the administrator is
allowed to retrieve OTP values for a given token.